Q-Day for Crypto: The Trillion-Dollar Security Reckoning
Crypto has faced hacks, exploits, and security failures for years, but one line of defence has always remained intact: the cryptography protecting private keys. Quantum computing could eventually change that, introducing a threat aimed not at weak code or human error, but at the mathematical foundations of the industry itself. While the danger is not immediate, the race to prepare has already begun. This report explains what is at stake, how close the technology really is, and why the transition may be harder than most expect. Let's dive in...
Every major crypto hack you can think of has one thing in common: somewhere along the line, someone made a mistake. The recent Drift exploit was another reminder of that reality. A vulnerability gets introduced, a process fails, or a system gets compromised. The damage can be severe, but the underlying cryptography, the actual math that protects your private keys, has never been broken.
Now imagine a future where that changes, and the lock itself no longer holds. Not because someone tricks you into handing over your keys, and not because a bug slips through in the code, but because a machine can reverse-engineer your private key from your public key using math alone.
That is the quantum threat, and Google Quantum AI just published a 57-page whitepaper explaining how this kind of attack would work and why it can no longer be treated as a theoretical problem.
This report breaks it down in plain English, no physics degree required.
In this report:
- What a quantum computer is and why it matters for crypto
- How the attack works and how close we really are
- What is at risk across Bitcoin, Ethereum, and crypto infrastructure
- What would likely break first, and why migration will be so difficult
- What it means for you right now
Disclaimer: This is not financial or investment advice. You are responsible for any capital-related decisions you make, and only you are accountable for the results.
Quantum Computers: The 60-Second Explainer
Before we get into the threat, it helps to understand what a quantum computer actually is. You do not need to understand the physics. You just need to understand why it matters.A regular computer thinks in bits. Each bit is either a 0 or a 1, and it solves problems by working through possibilities one at a time. Think of it like trying every key on a massive keyring until you find the right one. It works, but it becomes painfully slow when the number of possible keys grows large enough.
A quantum computer uses qubits instead of bits. A qubit can be 0, 1, or both at the same time, a property known as superposition. That allows a quantum computer to explore a far larger number of possibilities at once. Instead of checking each key one by one, it can approach the problem in a fundamentally different way.
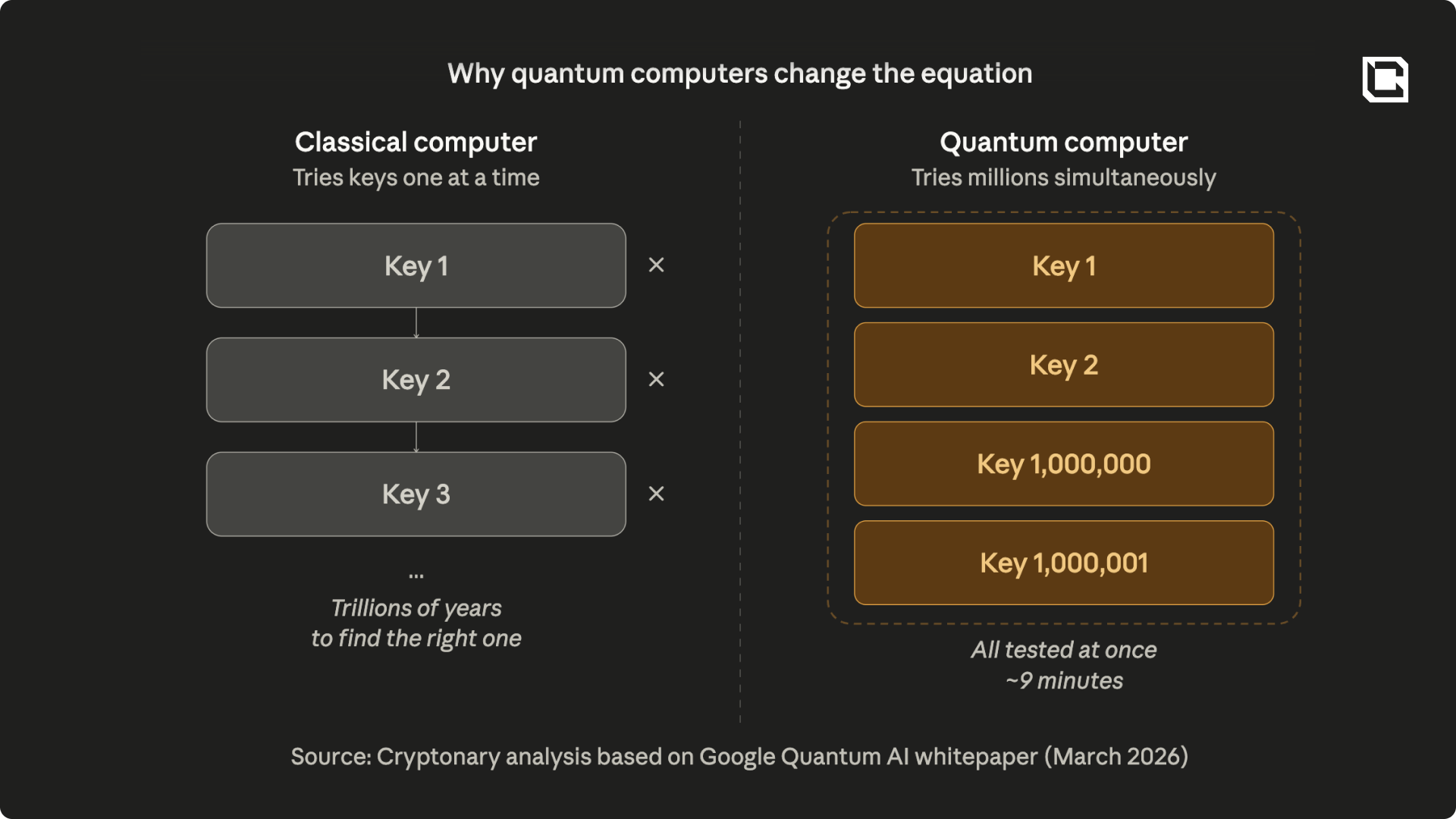
The qubit is the basic unit of quantum computing power, but not all qubits are equal. The hardware is noisy and error-prone, which means you need hundreds of physical qubits working together just to create one reliable logical qubit. Think of it like needing 400 unreliable employees to do the job of one expert. Google’s paper estimates that breaking crypto would require about 1,200 logical qubits, which translates to roughly 500,000 physical qubits. That is a 20x reduction from previous estimates.
One more point is worth understanding here: not all quantum computers are built the same way, and the architecture affects how dangerous they could be in practice. Some use superconducting circuits cooled to near absolute zero. These systems are fast, and companies like Google, IBM, and Rigetti are building them. Others use trapped atoms controlled by lasers.
Companies like IonQ and Quantinuum are pursuing that approach. These systems can be extremely precise, but they are much slower. A fast machine could crack a private key in about 9 minutes. A slower one might take anywhere from 14 hours to 12 days. That difference determines whether an attacker can only target wallets with keys already exposed on-chain, or whether they could also intercept live transactions in real time.
How Close Are We, Really?
Before going further, it is important to be clear about where things stand today. No quantum computer in existence can break the cryptography protecting any blockchain. The kind of machine Google describes, one with enough physical qubits, low enough error rates, and enough sustained stability to run a complex calculation for 9 to 23 minutes, does not exist today.Just as importantly, raw qubit count on its own does not mean much. The system also needs coherence, error correction, and the ability to sustain the entire computation long enough to finish it. Those are serious engineering challenges, and they have not been solved at the scale required to threaten crypto in the present moment.
So why does this matter now? Because we know tech tends to improve on an exponential scale. Even though viable quantum machines don’t exist today, the gap between theory and deployment is shrinking. Also, there will not be a public countdown clock telling the market when the threat has become real.
That uncertainty is part of the problem. The closer quantum systems get to commercial and strategic relevance, the less transparent development is likely to become. As Google notes, the first evidence that a meaningful breakthrough has arrived may not come through a press release, but through abnormal activity on-chain.
How the Attack Works
Your crypto wallet is protected by a mathematical problem known as the Elliptic Curve Discrete Logarithm Problem. Your public key and private key are mathematically related, but going from the public key back to the private key is so difficult that a classical computer would need longer than the age of the universe to solve it. In 1994, mathematician Peter Shor designed a quantum algorithm that could solve this type of problem efficiently. Thirty years later, the machines capable of running it are moving closer to feasibility.Google’s paper shows that a fast quantum computer could run the second half of Shor’s algorithm in about 9 minutes. The first half could be prepared in advance because it depends only on shared network parameters rather than any one user’s wallet.
On the other hand, Bitcoin’s average block time is about 10 minutes. You see the point? If you broadcast a transaction, an attacker could see your public key in the mempool, crack the private key, and try to submit a competing transaction before yours confirms. Under idealized conditions, the paper estimates the attacker could win that race roughly 41% of the time.
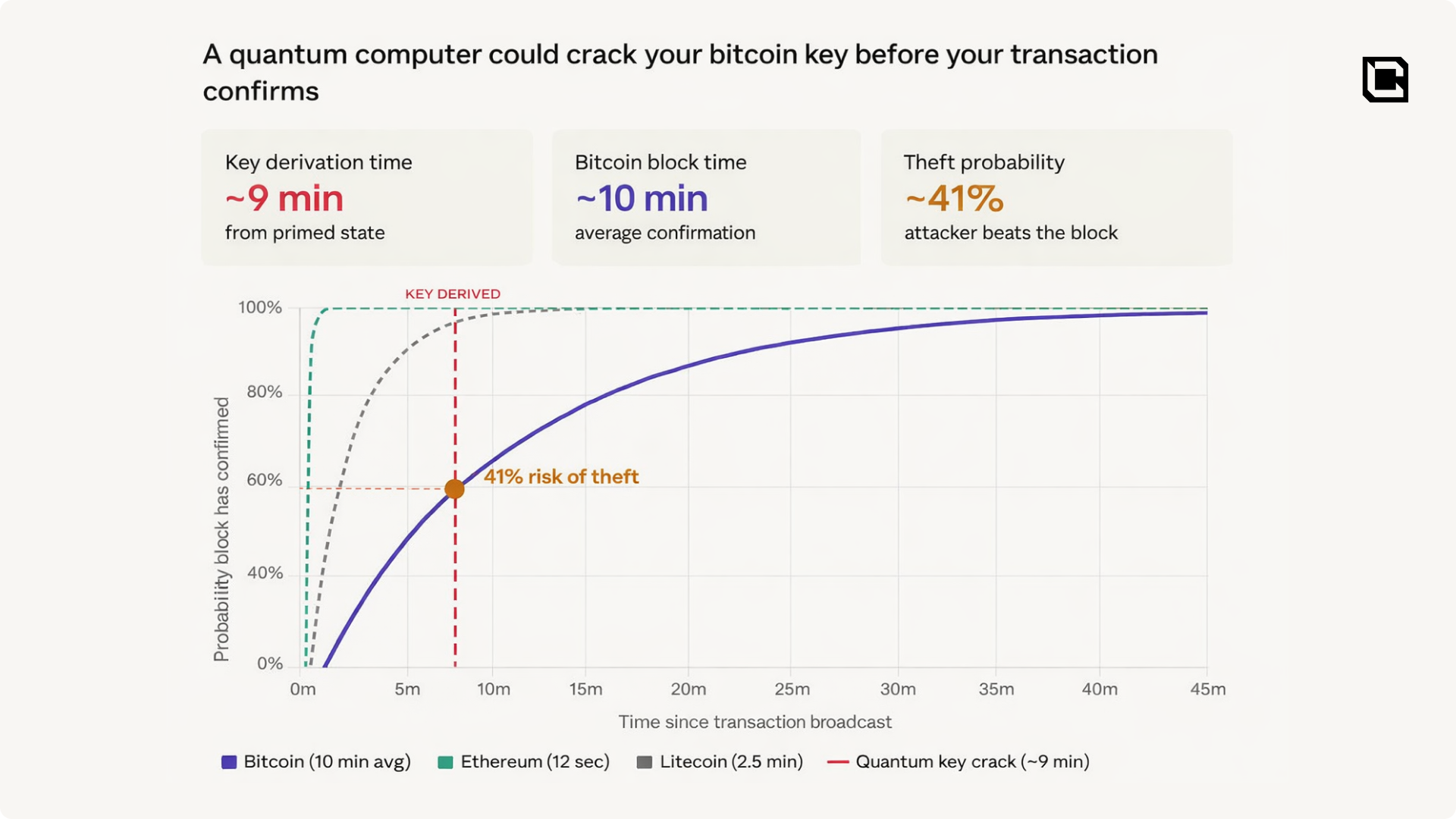
The paper separates the threat into two categories.
- “At-rest” attacks target public keys that are already exposed on the blockchain and give the attacker effectively unlimited time to crack them.
- “On-spend” attacks target live transactions and require the key to be cracked before the transaction is confirmed. That’s important because the timeline of the threat depends on what kind of quantum hardware arrives first. If fast machines come first, both attack types could emerge around the same time. If slower architectures arrive first, at-rest attacks may become possible years before on-spend attacks.
What’s at Risk?
Bitcoin
Not all Bitcoin addresses are equally vulnerable. In Bitcoin’s early years, some coins were stored in an older format that placed the full public key directly on-chain. Satoshi’s coins were mined this way, which is why roughly 1 million BTC are already sitting in addresses with permanently exposed public keys.Later address formats improved on this by hiding the public key behind a hash. That means if you use a modern Bitcoin address and have never spent from it, your public key is not yet visible on-chain. But once you spend from that address, the public key is revealed in the transaction. If any coins remain there afterward, those funds become exposed. This is the problem known as address reuse, and it is far more common than many people realize because large exchanges and custodians often do it for convenience.
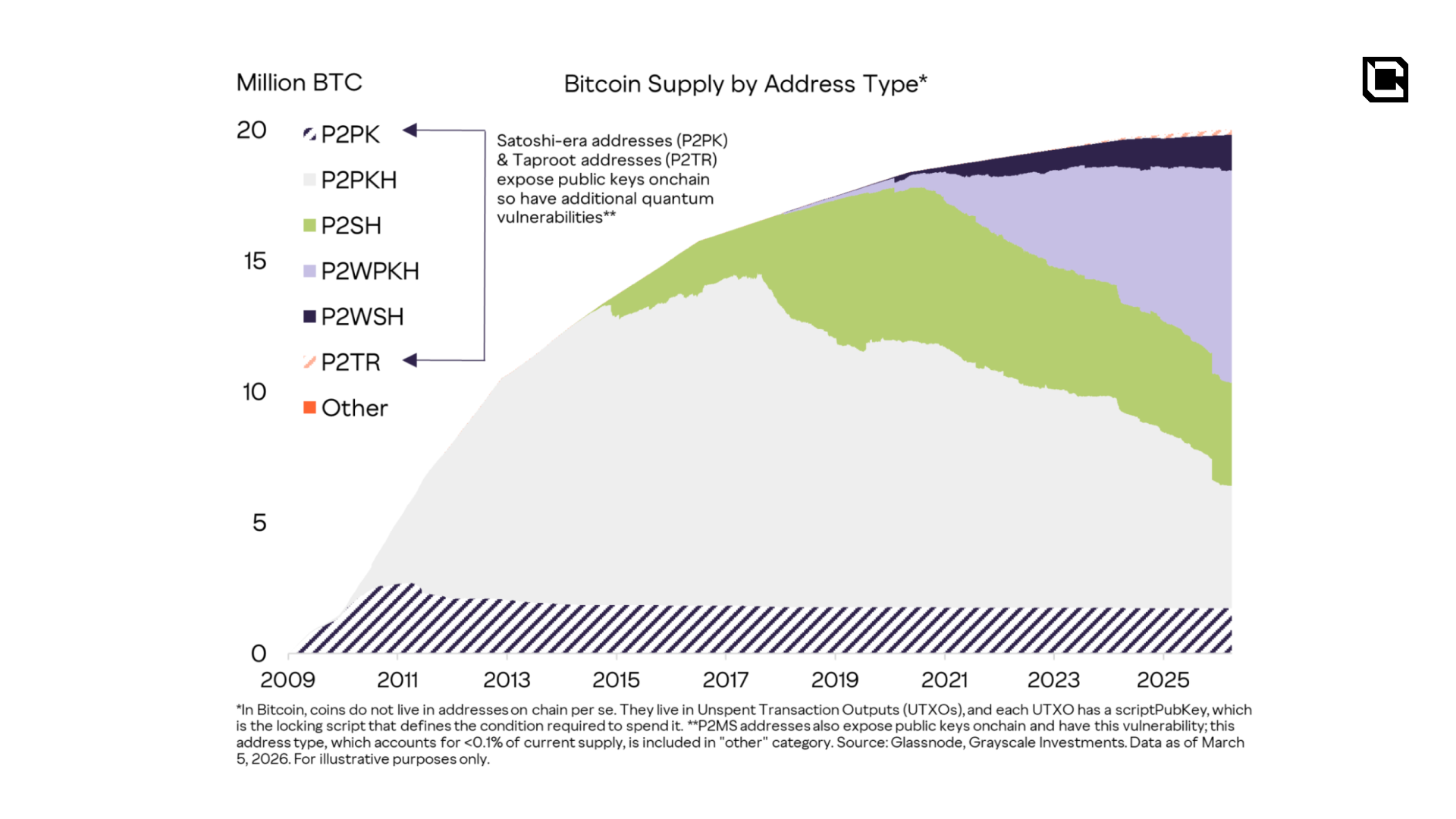
Roughly 1.7 million BTC sits in older exposed formats. Once address reuse is included, the amount of Bitcoin vulnerable to at-rest attacks rises to about 6.9 million BTC. Taproot, introduced in 2021, also brought back direct public key exposure in its newest address format, which adds another layer of quantum sensitivity. A proposed fix exists, but it has not been adopted yet.
The good news is that Bitcoin mining itself is not the issue here. Quantum computers do not offer a meaningful advantage over the dedicated mining hardware already used by the network today. The real risk is to exposed keys, not to Proof of Work itself.
Ethereum
Ethereum’s exposure looks different. Because of the way Ethereum accounts work, the first time an address sends a transaction, its public key is exposed on-chain permanently. Among the top 1,000 Ethereum accounts, roughly 20.5 million ETH is vulnerable on that basis alone.Furthermore, roughly $200 billion in stablecoins and tokenized real-world assets sits in smart contracts controlled by admin keys that are visible on-chain. If those keys were cracked, an attacker could mint unbacked tokens, freeze accounts, or drain bridges. On top of that, around 37 million staked ETH depends on a signature scheme that is also vulnerable to quantum attacks, and Ethereum’s data availability layer could face a different kind of risk altogether: a one-time break that creates a reusable backdoor.
Ethereum’s short block times make real-time on-spend attacks much harder under current assumptions, and its governance process is more capable of coordinating complex upgrades than Bitcoin’s. Even so, the attack surface is broader.
The Wider Ecosystem
The problem does not stop with Bitcoin and Ethereum. Stablecoins such as USDT and USDC depend on admin-controlled smart contracts. Tokenized real-world assets are expected to grow into the trillions, and much of that infrastructure will sit on the same vulnerable cryptographic foundation. Privacy chains such as Zcash and Monero face an additional problem, because even after they migrate, a future quantum attacker could still decrypt years of old transaction history. Bridges and Layer 2s inherit the weaknesses of the chains beneath them while often introducing new ones of their own.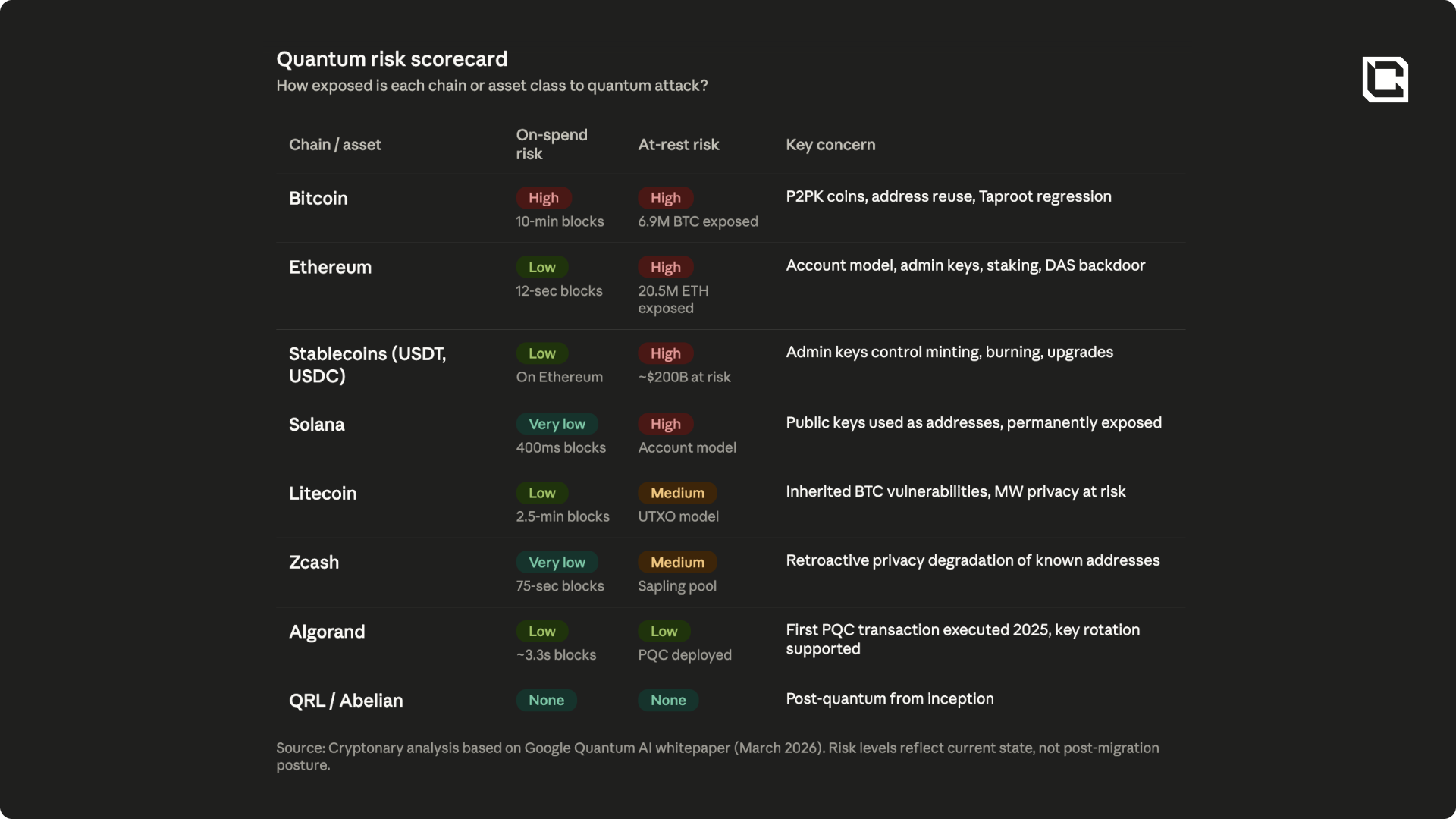
What Would Likely Break First
If a quantum computer capable of breaking today’s public-key cryptography appeared tomorrow, the first impact would probably not come from random retail wallets being drained one by one. The first wave of fear, and likely the first wave of real damage, would center where a small number of keys control a very large amount of value.That is why the most immediate pressure would likely fall on admin keys tied to bridges, stablecoin issuers, and major DeFi protocols. There are not many of these keys, but each one controls an outsized amount of value. Cracking a single one could drain a bridge, compromise a critical smart contract, or disrupt infrastructure that other protocols depend on. In a tightly connected DeFi environment, the damage would not stay isolated for long.
The next point of stress would likely be custodians, exchanges, and ETF infrastructure. Most mainstream capital sits with Coinbase, Binance, ETF custodians, and institutional trading firms managing large pools of assets through hot wallets, reused addresses, and multisig systems that were not designed for a post-quantum world.
After that, dormant Bitcoin with exposed public keys would become an obvious target. That includes Satoshi’s coins and other older outputs whose keys are already visible on-chain.
A reasonable way to think about the order of risk is this: admin keys and bridges first, custodians and exchanges second, dormant exposed Bitcoin third, consensus and protocol-layer attacks fourth, and retroactive privacy degradation on privacy chains fifth.
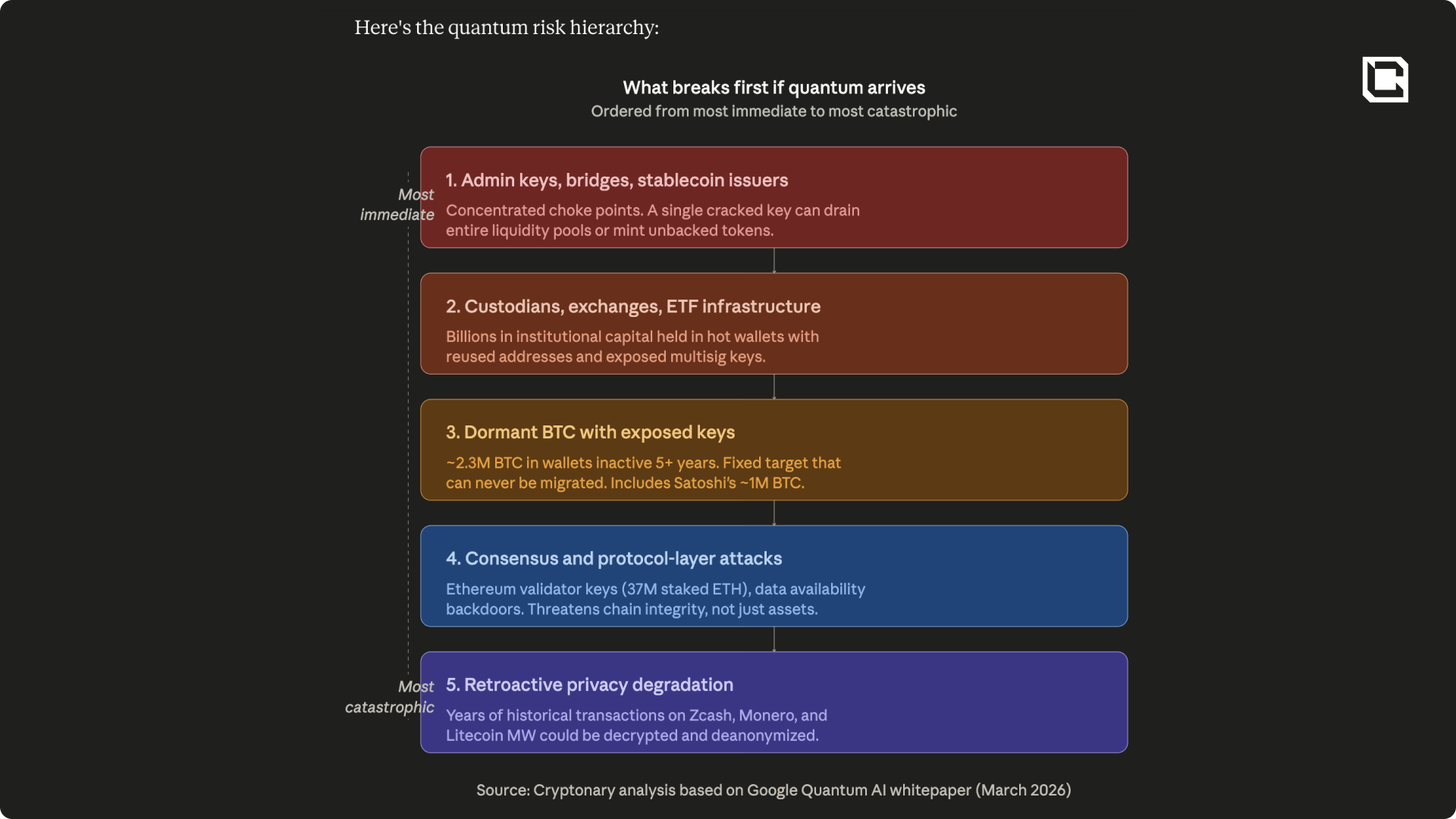
The Satoshi Problem
Roughly 2.3 million BTC sits in wallets that have not moved in over five years and have exposed public keys. In many of these cases, the keys are likely lost forever, which means the coins cannot be migrated to a quantum-safe format even if the rest of the network is ready.That creates a uniquely difficult problem for Bitcoin. These coins are not just vulnerable. They are a fixed, multi-hundred-billion-dollar target that may eventually become accessible to whoever gets there first.
The Bitcoin community is now debating three main responses:
One is to do nothing and leave the protocol unchanged, allowing whoever builds a sufficiently powerful quantum computer first to claim the coins. That preserves property rights, but risks major price volatility and a large supply shock.
Another is to burn them by making them permanently unspendable after a certain date. That would reduce the shock, but it would also amount to confiscation.
A third option, sometimes called “Hourglass,” would not confiscate the coins or make them unspendable. Instead, it would limit how quickly dormant wallets with exposed keys could be spent, for example by only allowing a small number of them to move in each block or over a given period. The idea is to prevent a sudden flood of old Bitcoin from hitting the market all at once, reduce the immediate price shock, and force quantum attackers to compete over time rather than claim everything instantly.
Google’s paper proposes a fourth path: a “Bad Sidechain” where quantum-recovered coins would be sent for resolution using off-chain proofs of ownership such as seed phrases. It is the most nuanced approach, but also the most complex.
There is no consensus on which path Bitcoin should take. An informal poll at the 2025 Presidio Bitcoin Quantum Summit split opinion roughly evenly across the main options, and the 2017 block size war that led to Bitcoin Cash is a reminder of what happens when the network cannot agree on a high-stakes change.
Why Migration Is Harder Than It Sounds?
The fix for the quantum threat is straightforward in theory: move from today’s cryptography to post-quantum cryptography. The hard part is everything that comes after that sentence. Saying “just swap the signatures” makes the transition sound simple when it is anything but.The first issue is size. The cryptographic signatures used by Bitcoin and Ethereum today are relatively small. Post-quantum alternatives are much larger, which means they take up more space in each block. If Bitcoin adopted them without changing anything else, fewer transactions would fit and throughput would fall. If the network tried to solve that by increasing capacity, it could run straight back into the same kind of political and governance tensions that split the Bitcoin community in 2017.
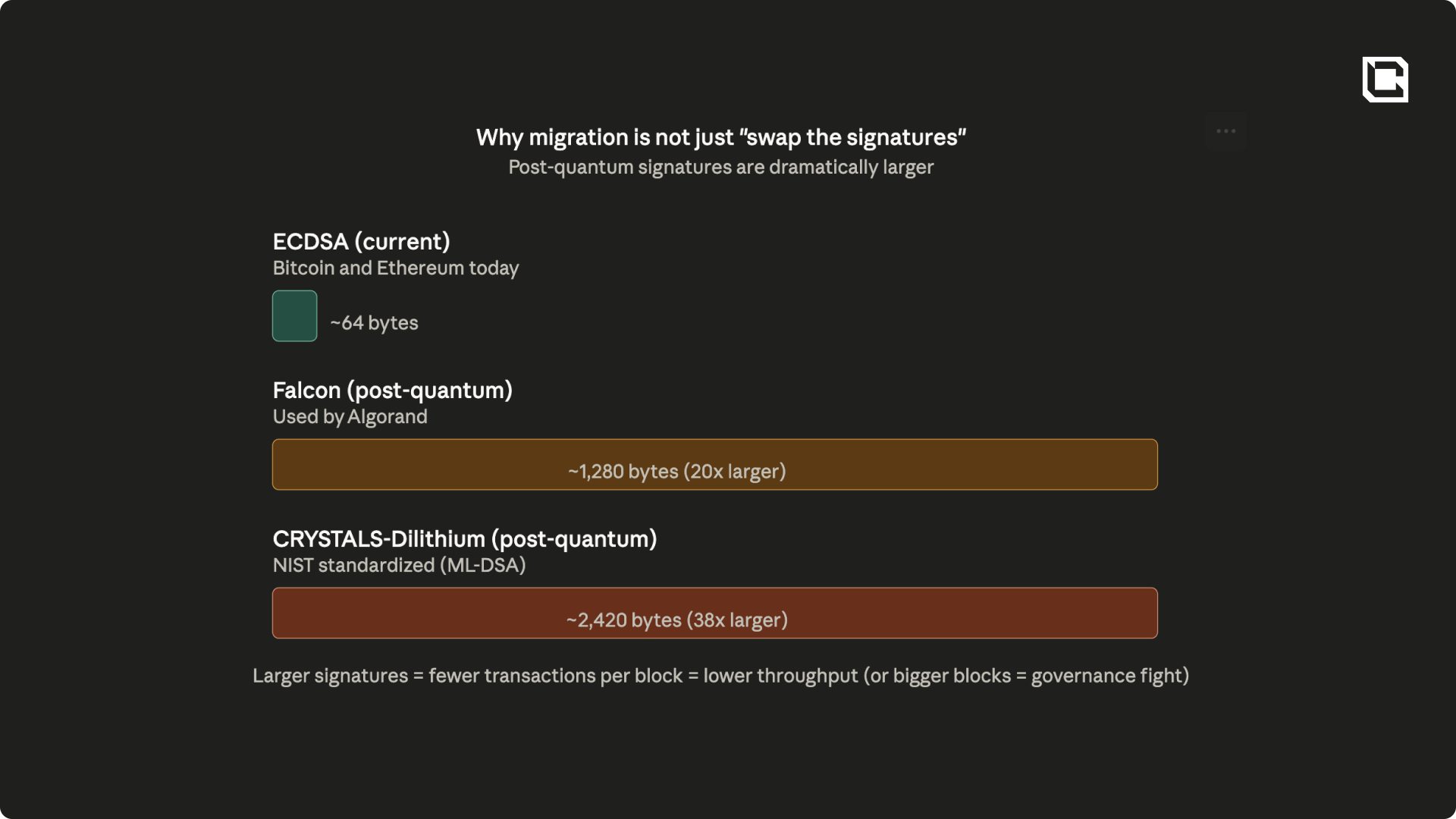
The challenge also goes far beyond the base layer. Every wallet, hardware device, exchange integration, bridge, Layer 2, multisig setup, and custody system would need to be updated. Ledger and Trezor devices would need new firmware. Exchanges would need to rebuild parts of their signing infrastructure. Existing smart contracts on Ethereum cannot simply be patched all at once. Each protocol team would need to coordinate its own migration, and every step of that process would create operational risk.
Then there is the migration window itself. Even once the standards are ready and the technical path is clear, assets still need to be moved from vulnerable addresses and key schemes to safer ones. A transition of that scale would take time. On Bitcoin in particular, the process would not happen overnight. It would likely unfold over months, and during that period anyone who had not yet moved would remain exposed.
It is also worth understanding that this is not a crypto-specific problem. The same class of cryptography that protects Bitcoin wallets also secures large parts of the internet, cloud systems, banking infrastructure, government networks, and enterprise security. Crypto may be one of the first places where the consequences would be visible in public, but the eventual hardening effort will reach far beyond blockchains.

The difference is that banks, tech companies, and governments can mandate upgrades from the top down. Public blockchains cannot. They need agreement across developers, validators, exchanges, infrastructure providers, and users, all of whom move at different speeds and have different incentives. That coordination layer is the real bottleneck, which is exactly why crypto needs to start earlier, not later.
None of this means the industry is incapable of meeting the challenge. Some of the strongest protocol engineers in the world are already working on this problem, and crypto has solved hard technical problems before. Ethereum’s move from proof of work to proof of stake showed that a major live upgrade can be executed at global scale without stopping the network. A post-quantum migration would be even more difficult, but the broader point still holds: this industry has a history of solving hard technical problems in public, and there is no reason to think this one will be any different.
Who's Already Preparing
This is no longer a niche discussion happening at the edges of crypto. Serious work is already underway, and some of the largest and most credible players in the industry are now treating post-quantum security as a real long-term issue rather than a theoretical curiosity.Coinbase launched an independent quantum advisory board in January 2026, bringing the issue into the open at the level of major exchange and custody infrastructure. The Ethereum ecosystem is also actively working on the problem through both its broader roadmap and its dedicated cryptography research efforts, which now explicitly include post-quantum security. And outside crypto, the fact that post-quantum standards have already been finalized tells you this is not a speculative thought experiment. The transition has already started.

Even Michael Saylor has had to address the issue publicly. He has argued that the threat is not immediate and that Bitcoin will have time to adapt, which is a reasonable view. But the more important point is that the conversation has clearly moved beyond researchers and protocol specialists. When figures like Saylor are talking about quantum risk at all, it is a sign that the subject has entered the mainstream of Bitcoin debate.
That does not mean quantum computers are about to arrive next year. It means the industry increasingly understands that the harder problem is the transition itself. A migration of this scale will take years, require coordination across multiple layers of infrastructure, and cannot be improvised once the pressure becomes real.
Cryptonary's Take
If you are reading this today, your crypto is not under immediate threat from quantum computing. No machine in existence can break the cryptography protecting today’s blockchains, so there is no reason to make drastic changes overnight.That being said, this is still a risk worth understanding today, because it is important to stay informed whenever emerging technologies have the potential to affect large amounts of capital and critical infrastructure.
For individual users, the priority is staying informed, watching how the major chains, custodians, exchanges, and infrastructure providers prepare, and being ready to follow clearer guidance when the time comes. Any real transition will happen through protocol upgrades, wallet support, custody changes, and coordinated migration paths, not through retail users improvising their own solutions years in advance.
It’s also worth addressing one of the most common myths circulating on social media. Some argue that if quantum computers break asymmetric cryptography, we will have bigger problems than compromised crypto (e.g. banks, the internet, payment networks, and military systems)
However, centralized entities can migrate to post-quantum algorithms more easily and can even reverse or mitigate damage from quantum-related breaches. Public blockchains, by contrast, face a more complex challenge: millions of users would need to manually migrate funds to quantum-resistant addresses, while validators and developers coordinate large-scale protocol upgrades.
That said, solutions will likely emerge. If there is one reliable motivator, it is economic self-interest. The crypto community will have strong incentives to coordinate, upgrade, and, if necessary, agree on forks to protect their “bags”.
The important work is already underway, which is exactly why this issue deserves attention today rather than panic tomorrow. And when the implications become more immediate, Cryptonary will be here to separate signal from noise and explain what actually matters.
Cryptonary, OUT!
Continue reading by joining Cryptonary Pro
$1,548 $997/year
Get everything you need to actively manage your portfolio and stay ahead. Ideal for investors seeking regular guidance and access to tools that help make informed decisions.
For your security, all orders are processed on a secured server.
As a Cryptonary Pro subscriber, you also get:
24/7 access to experts with 50+ years’ experience Terms
All of our top token picks for 2025
On hand technical analysis on any token of your choice
Weekly livestreams & ask us anything with the team
Daily insights on Macro, Mechanics, and On-chain
Curated list of top upcoming airdrops (free money)
Our track record speaks for itself
With over 2.4M tokens and widespread misinformation in crypto, we cut through the noise and consistently find winning assets.
Our track record speaks for itself
With over 2.4M tokens and widespread misinformation in crypto, we cut
through the noise and consistently find winning assets.
Frequently Asked Questions
Can I trust Cryptonary's calls?
Yes. We've consistently identified winners across multiple cycles. Bitcoin under $1,000, Ethereum under $70, Solana under $10, WIF from $0.003 to $5, PopCat from $0.004 to $2, SPX blasting past $1.70, and our latest pick has already 200X'd since June 2025. Everything is timestamped and public record.
Do I need to be an experienced trader or investor to benefit?
No. When we founded Cryptonary in 2017 the market was new to everyone. We intentionally created content that was easy to understand and actionable. That foundational principle is the crux of Cryptonary. Taking complex ideas and opportunities and presenting them in a way a 10 year old could understand.
What makes Cryptonary different from free crypto content on YouTube or Twitter?
Signal vs noise. We filter out 99.9% of garbage projects, provide data backed analysis, and have a proven track record of finding winners. Not to mention since Cryptonary's inception in 2017 we have never taken investment, sponsorship or partnership. Compare this to pretty much everyone else, no track record, and a long list of partnerships that cloud judgements.
Why is there no trial or refund policy?
We share highly sensitive, time-critical research. Once it's out, it can't be "returned." That's why membership is annual only. Crypto success takes time and commitment. If someone is not willing to invest 12 months into their future, there is no place for them at Cryptonary.
Do I get direct access to the Cryptonary team?
Yes. You will have 24/7 to the team that bought you BTC at $1,000, ETH at $70, and SOL at $10. Through our community chats, live Q&As, and member only channels, you can ask questions and interact directly with the team. Our team has over 50 years of combined experience which you can tap into every single day.
How often is content updated?
Daily. We provide real-time updates, weekly reports, emergency alerts, and live Q&As when the markets move fast. In crypto, the market moves fast, in Cryptonary, we move faster.




















